Examples On Computer Network Research Papers.
View Computer Networks Research Papers on Academia.edu for free.
We examples on computer network research papers would never take your money if we feel that we examples on computer network research papers cannot do your work. However, such a situation is a rarity with us. With our custom essay offer, you can be sure to get any type of essay help you are looking for. At 6DollarEssay.com, just tell us what you.
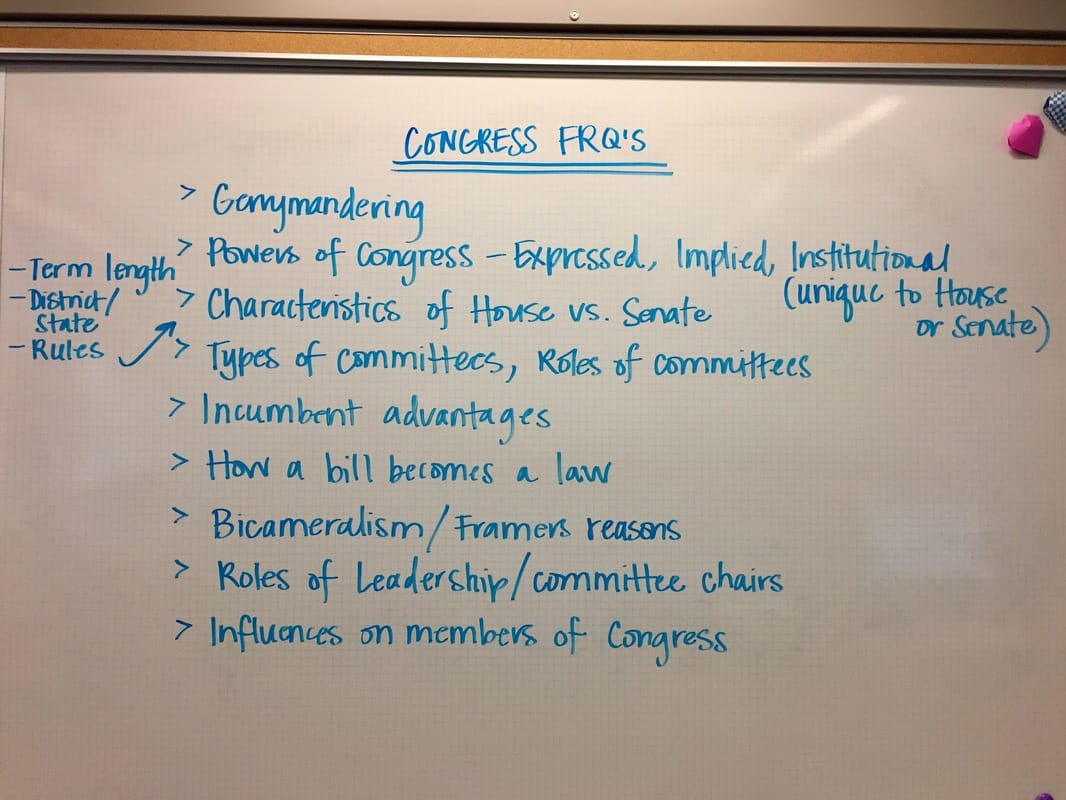
It has become an essential omnipresent technology with explosive growth. There are ample of books accessible for the study and design of computer networks. This paper addresses Components of Computer Networking (LAN) free download S Nowell ece.gatech.edu Computer networks are classified by scale, components, and connection method.
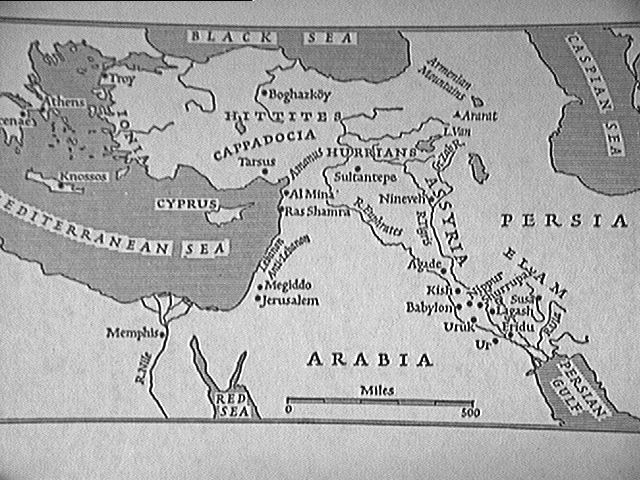
Large scale computer networks are very complex systems. As the size of a. Figure 2.1: An example network showing a ow of data. Inference is the ability of a system to reason around facts and to draw con-. papers written about the concept (5, 8, 25, 21, 22). All of these papers either.

Computer forensics involves the preservation, identification, extraction, documentation and interpretation of computer data (Kruse II and Heiser 2002). Computer forensics is usually used when a crime has been committed or an inappropriate activity has taken place. Some common examples of when computer forensics is used are.

Once production of your article has started, you can track the status of your article via Track Your Accepted Article. CiteScore measures the average citations received per document published in this title. CiteScore values are based on citation counts in a given year (e.g. 2015) to documents published in three previous calendar years (e.g.

The primary purpose of Computer Networks is to publish original and complete research papers covering a specific topic or project in the above-mentioned areas in sufficient detail and depth to be of practical use to interested readers.

Computer and phases of Research Research process has five major phases (3).Computer can be used in these following phases. Conceptual Phase and Computer In this phase, formulation of research problem, review of literature, theoretical frame work and formulation of hypothesis. Computer helps in searching the existing literature.
The whole network has been installed in real and test bed has been used for results. The network was continuously monitored for fine tunings. The outcome of Network monitoring and users’ feedback are as follows. 1. Though the Wi-Fi is signals are available in each house, but they are limited to the rooms facing the antenna only.

COMPUTER NETWORKING AND MANAGEMENT In a computer network management system, there should be a method for getting computer programs ready for execution, in relation to particular network devices. Every device in the network is associated with a device type value, and must have an associated device mapper. These device mappers are arranged in a hierarchical structure to show a family or.

What follows is a hypothetical example of a research paper based on an experiment. The experiment: Say you have just conducted the Milgram Study. Now you want to write the research paper for it. (Milgram actually waited two years before writing about his study.) Here's a shortened example of a research article that MIGHT have been written.

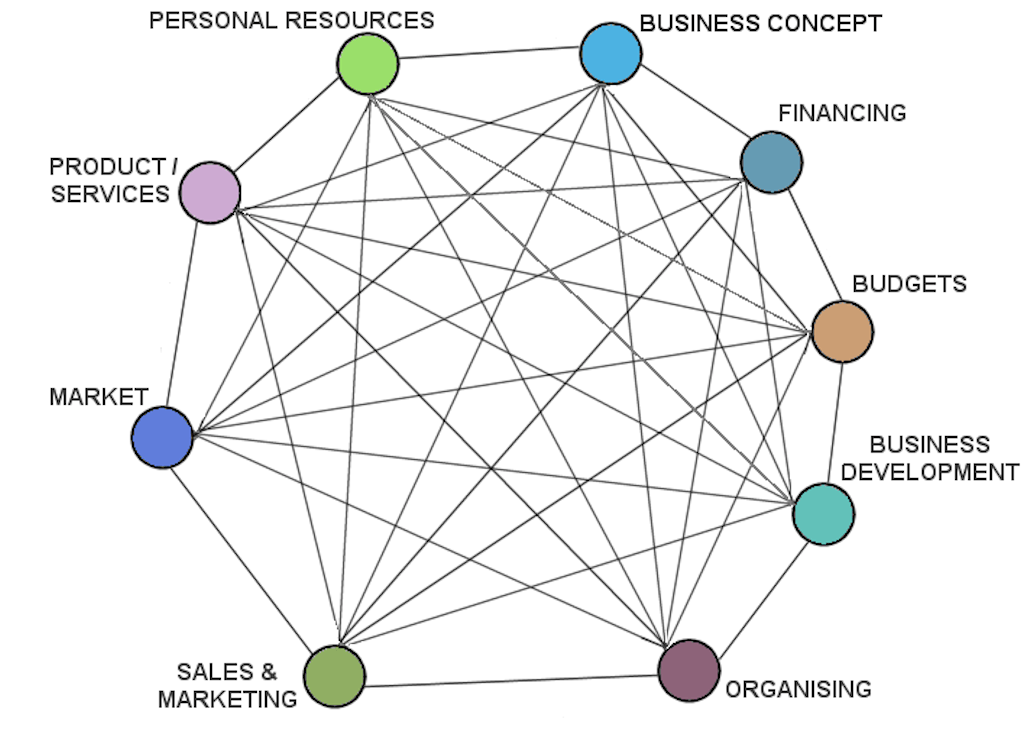
Computer networking is the interconnection of two or more computers to share resources. Computer networking has evolved beyond the sharing of resources; it allows people and machines to communicate, using some of the advanced features or services. Computer networking has brought about increased productivity, cost reduction and synergy between.
Research Proposal Example 3 (DOC, 55.5kB) Research Proposal Example 4 (DOC, 49.5kB) Your research proposal is an integral part of the Research Degree application process, and as such, it is worth investing time and energy to ensure that your proposal is strong, clear and effective. Your proposal needs to outline the nature of your proposed.